Introduction
Imagine waking up to find your manufacturing operations halted because of a cyber attack. Sounds scary, right? In an industry increasingly reliant on digital technologies, the intersection of cybersecurity and manufacturing is crucial. As we dive into digital transformation, the stakes are high. Just think about it: one cyber incident could cost millions and throw everything into chaos.
In this article, we’ll explore some best practices for keeping your digital transformation secure. We’ll look at how to weave cybersecurity into your business strategies, prioritize security measures, and encourage teamwork between IT and operations. With cyber threats changing faster than ever, the big question is: how can manufacturers protect their assets while still pushing for innovation?
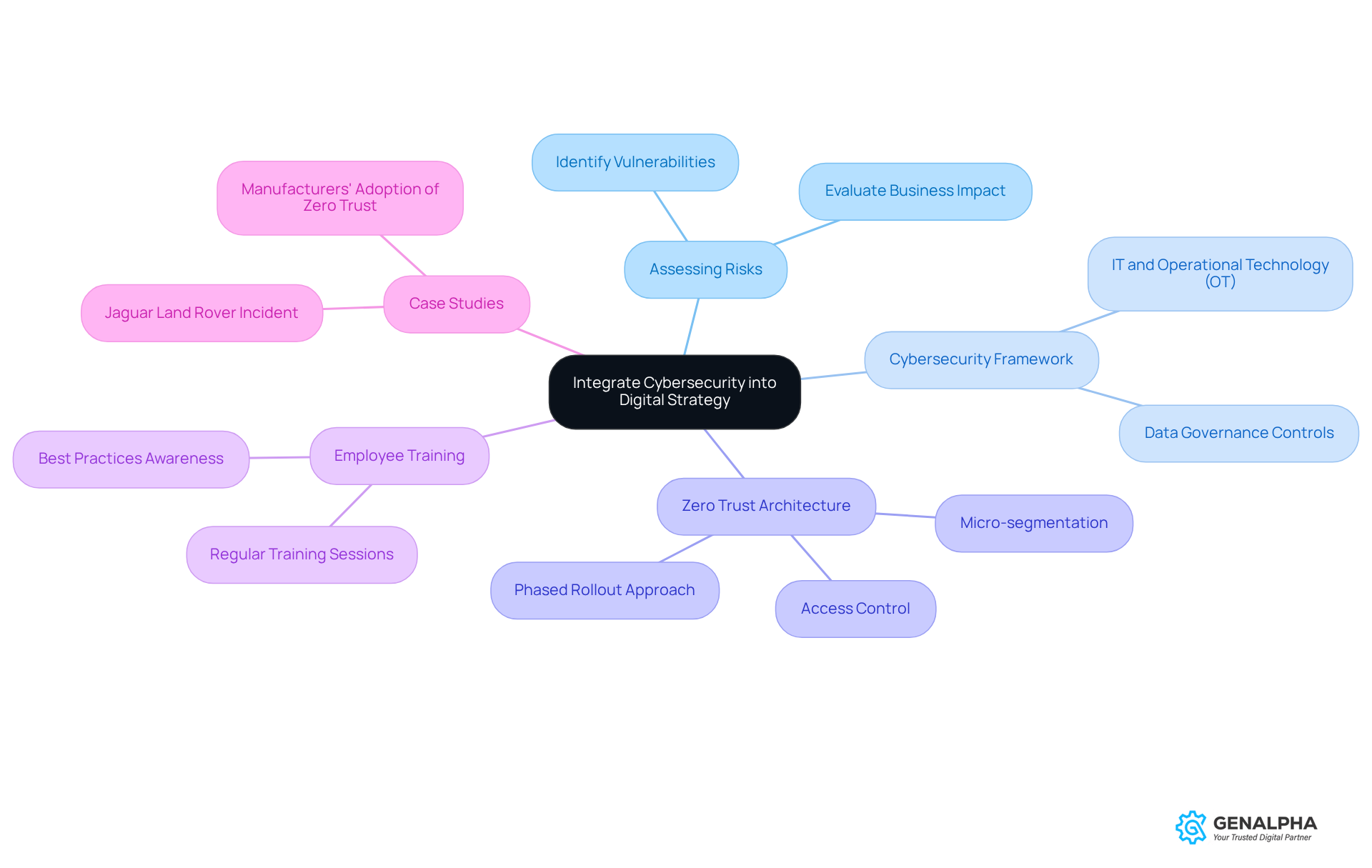
Integrate Cybersecurity into Digital Strategy
Have you ever thought about how your cybersecurity measures stack up against your business goals? To effectively implement protective measures in your secure digital transformation plan, it’s crucial to align them with what your business aims to achieve. Start by assessing the risks to spot any vulnerabilities in your digital setup. You’ll want to think about a cybersecurity framework that covers both IT and operational technology (OT). For instance, adopting a Zero Trust architecture means every access request gets a thorough check, no matter where it comes from. This approach helps cut down risks from outdated measures and boosts your resilience against cyber threats.
But it doesn’t stop there! Promoting a culture of awareness through regular employee training on best practices is key. Experts like Cooper say that when your protective strategies align with your business goals, you’re not just protecting assets; you’re also paving the way for secure digital transformation and growth. Did you know that the average total cost of a ransomware incident in manufacturing hit around $8.7 million in 2024? That’s a hefty price tag for not having solid cybersecurity in place.
Additionally, case studies show how manufacturers maintain production continuity even when facing rising cyber threats by using Zero Trust principles. So, in a world where cyber threats are on the rise, can you afford to leave your business unprotected?
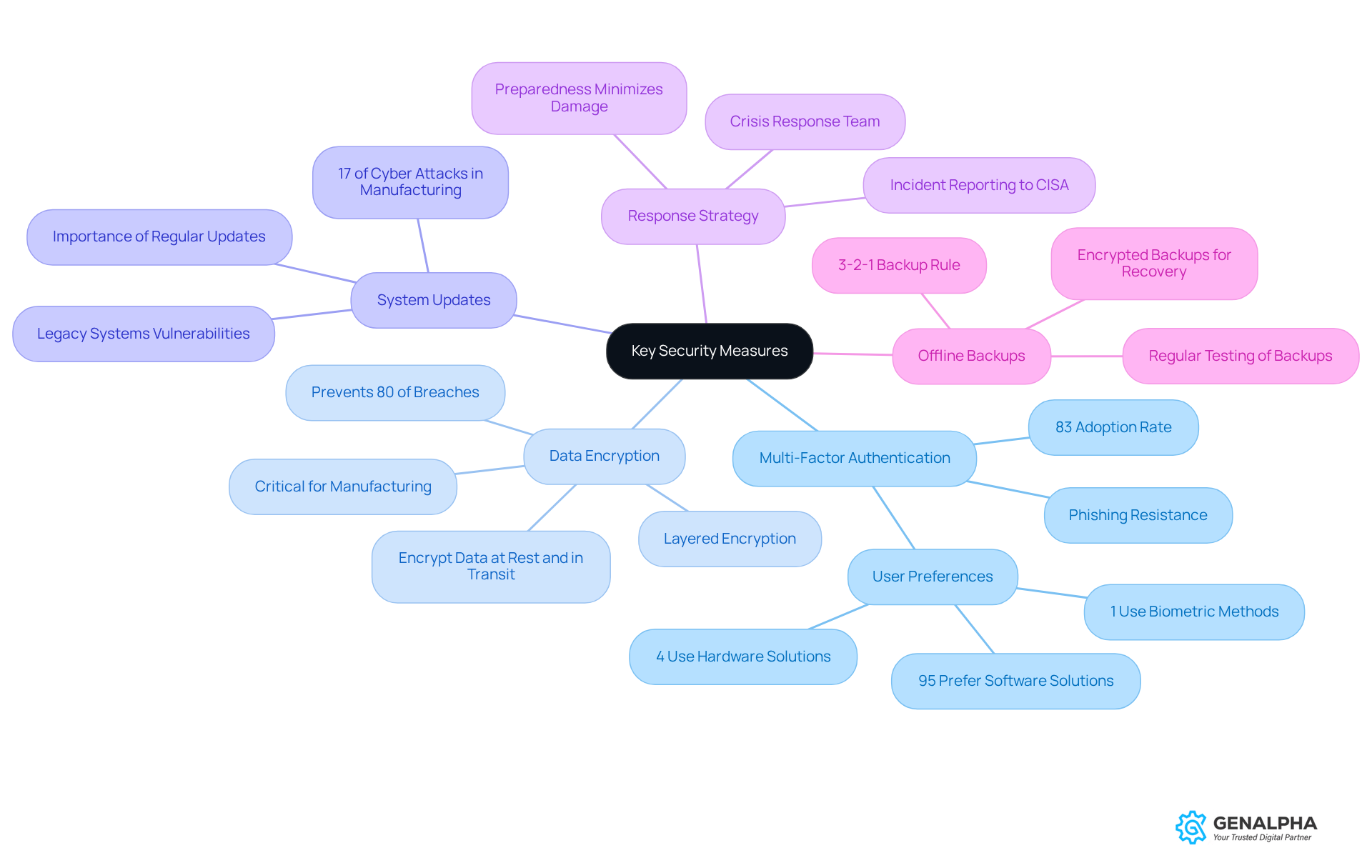
Prioritize Key Security Measures
Ever thought about how secure your organization really is against cyber threats? Let’s talk about how you can beef up your security-starting with multi-factor authentication (MFA) across all your systems. It’s a simple way to add an extra layer of defense against unauthorized access. In fact, 83% of organizations are already on board with MFA, showing just how important it is to keep sensitive information safe.
Plus, don’t forget about data encryption! It’s key to keeping your critical info safe, whether it’s on the move or sitting still. Unencrypted data is like leaving your front door wide open for attackers. Keeping your software and systems up to date is super important. Did you know that manufacturing saw a jump to 17% of cyber attacks in 2024? That’s up from 9% just the year before!
Having a solid response strategy means you can tackle any security breaches quickly, minimizing the damage. It’s all about being prepared! And hey, don’t forget about offline, encrypted backups! They’re your safety net for recovery if something goes wrong. Organizations that have taken these steps are seeing a big drop in successful cyberattacks. It just goes to show how effective a proactive security approach can be! By taking these steps, you’re not just protecting data; you’re safeguarding your entire operation from potential disaster.
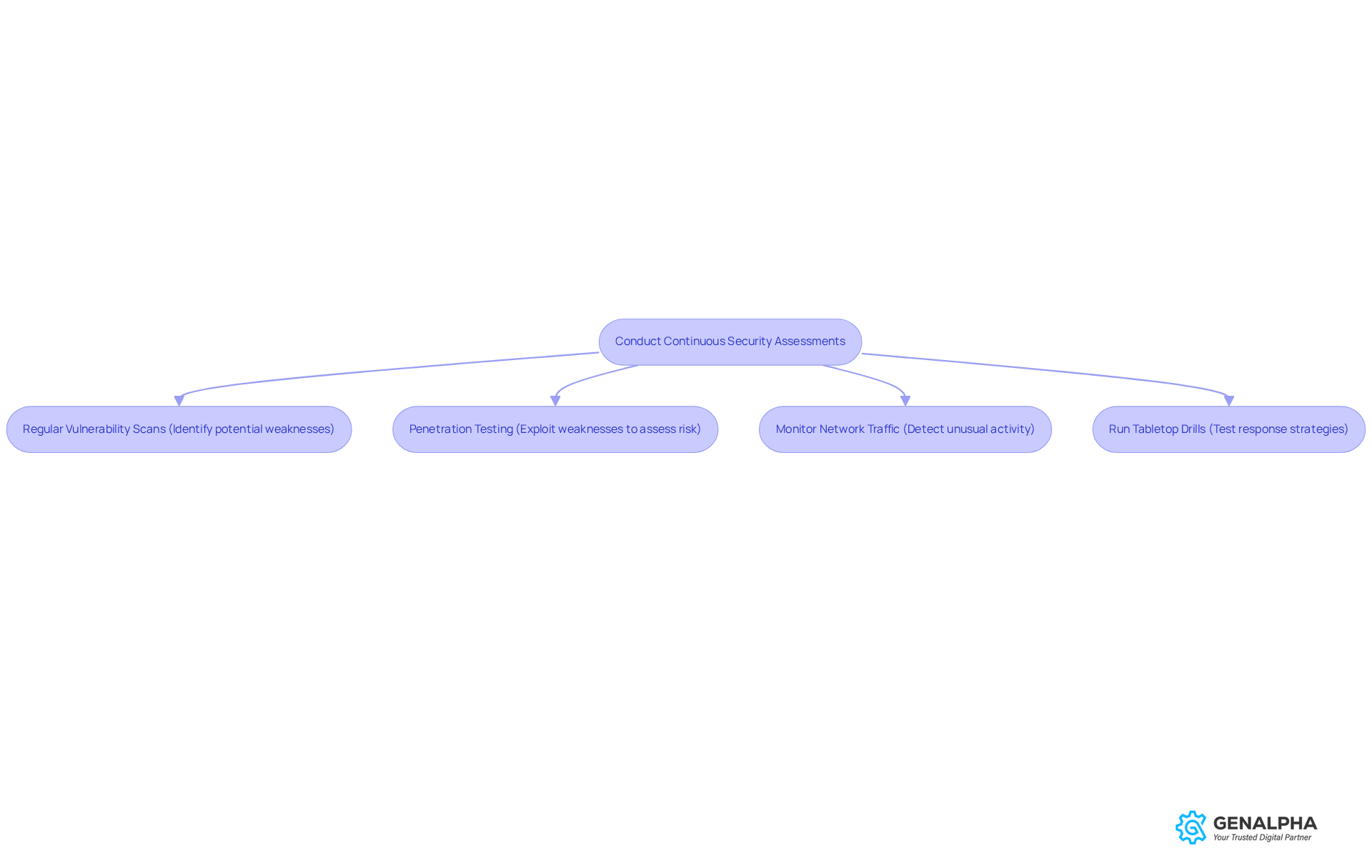
Conduct Continuous Security Assessments
Are you confident that your cybersecurity plan is up to date? Ongoing safety evaluations should be a key part of it. Regular vulnerability scans and penetration testing can help you spot weaknesses in your systems before they become a problem.
Use automated tools to keep an eye on network traffic for any unusual activity that might signal a breach. Additionally, running tabletop drills with your protective and operations teams can prepare you for real incidents by testing your response strategies.
Without regular checks, your systems could be vulnerable to attacks that might go unnoticed until it's too late. Organizations that embrace continuous evaluation can adjust more quickly to new threats, ensuring they stay one step ahead. Staying ahead of threats isn't just smart; it's essential for your organization's survival.
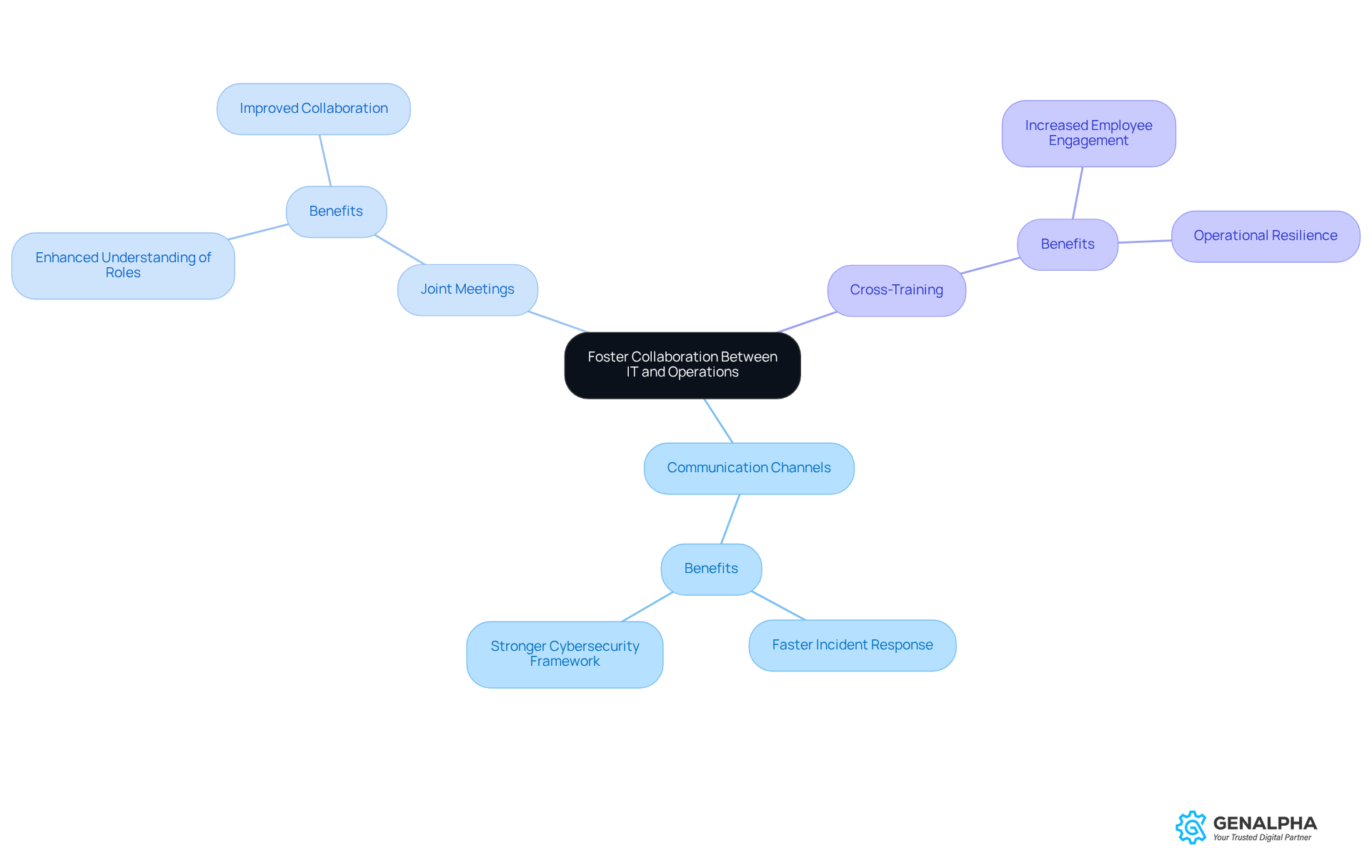
Foster Collaboration Between IT and Operations
Have you ever felt like IT and operations are speaking different languages? Creating consistent communication channels and holding joint meetings can really bridge that gap. Plus, cross-training can help everyone understand each other's roles better, making it easier to work together.
And guess what? Companies that have brought IT and OT teams together often see faster incident response times and a stronger approach to secure digital transformation. Interestingly, 40% of manufacturers say that concerns about secure digital transformation hold them back from adopting AI, which shows just how important collaboration is.
So, let’s break down those silos and work together to create a stronger cybersecurity framework that enables secure digital transformation and can handle new threats!
Conclusion
In a world where cyber threats are lurking around every corner, manufacturers can't afford to overlook cybersecurity. Integrating strong cybersecurity measures into digital transformation strategies is key for manufacturers who want to thrive in today’s digital landscape. By aligning cybersecurity with business goals, organizations not only protect their assets but also create an environment ripe for innovation and growth. The focus on frameworks like Zero Trust shows just how important it is to scrutinize every access request, significantly reducing risks tied to outdated security practices.
Key practices like:
- Multi-factor authentication
- Data encryption
- Ongoing security assessments
form the backbone of a resilient cybersecurity strategy. These steps not only protect sensitive information but also boost the organization’s ability to respond quickly to potential threats. Plus, when IT and operations teams collaborate, it strengthens the overall approach, ensuring everyone is on the same page in the fight against cyber threats.
At the end of the day, prioritizing cybersecurity in manufacturing is crucial. As cyber threats keep evolving, manufacturers must take a proactive stance, embracing best practices and fostering collaboration. Failing to act could lead to devastating breaches that cripple operations. Now’s the time to act! Protecting the future of manufacturing means committing to a solid cybersecurity approach.
Frequently Asked Questions
Why is it important to integrate cybersecurity into a digital strategy?
Integrating cybersecurity into a digital strategy is essential to align protective measures with business goals, ensuring that vulnerabilities are addressed and risks are minimized during digital transformation.
What steps should be taken to assess cybersecurity risks?
Start by assessing the risks to identify any vulnerabilities in your digital setup, which will help in implementing effective protective measures.
What is a cybersecurity framework and why is it necessary?
A cybersecurity framework is a structured approach that outlines security measures for both IT and operational technology (OT). It is necessary to ensure comprehensive protection against cyber threats.
What is Zero Trust architecture?
Zero Trust architecture is a security model that requires thorough verification of every access request, regardless of its origin, to reduce risks associated with outdated security measures.
How can employee training contribute to cybersecurity?
Regular employee training on best practices promotes a culture of awareness, which is crucial for strengthening cybersecurity measures and protecting assets.
What is the financial impact of ransomware incidents in manufacturing?
The average total cost of a ransomware incident in manufacturing reached around $8.7 million in 2024, highlighting the importance of having solid cybersecurity measures in place.
How have manufacturers used Zero Trust principles to maintain production continuity?
Case studies show that manufacturers employing Zero Trust principles have been able to maintain production continuity even when facing increasing cyber threats.
What are the consequences of not having strong cybersecurity in place?
Without strong cybersecurity measures, businesses risk significant financial losses, operational disruptions, and exposure to cyber threats, which can jeopardize their growth and stability.
List of Sources
- Integrate Cybersecurity into Digital Strategy
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Manufacturing in the Crosshairs: How Zero Trust Architecture Secures the Future of Smart Factories (https://govinfosecurity.com/whitepapers/manufacturing-in-crosshairs-how-zero-trust-architecture-secures-w-16178)
- Who Can You Trust? (https://advancedmanufacturing.org/smart-manufacturing/who-can-you-trust/article_6379fbc6-745f-11ef-9ad5-ebeed110df32.html)
- Why Manufacturing CIOs Are Extending Zero Trust Inside the Factor (https://zscaler.com/blogs/product-insights/why-manufacturing-cios-are-extending-zero-trust-inside-factory)
- Manufacturing Cyber Attack Statistics 2026: Data-Driven Insights on Industrial Security Threats (https://totalassure.com/blog/manufacturing-cyber-attack-statistics-2026-data-driven-insights-on-industrial-security-threats)
- Prioritize Key Security Measures
- Level Up Your Defenses—Four Cybersecurity Best Practices for Businesses | CISA (https://cisa.gov/resources-tools/resources/level-your-defenses-four-cybersecurity-best-practices-businesses)
- 2025 Multi-Factor Authentication (MFA) Statistics & Trends to Know (https://jumpcloud.com/blog/multi-factor-authentication-statistics)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)
- Data Encryption for Manufacturing - Securing Your Data (https://acoupleofgurus.com/data-encryption-for-manufacturing)
- Conduct Continuous Security Assessments
- 95% of Enterprises Prioritize Pentesting, Yet Only 32% of Attack Surfaces Are Tested, New Synack and Omdia Research Finds (https://prnewswire.com/news-releases/95-of-enterprises-prioritize-pentesting-yet-only-32-of-attack-surfaces-are-tested-new-synack-and-omdia-research-finds-302718985.html)
- Vulnerability Statistics 2026: Key Trends & Data | Indusface (https://indusface.com/blog/key-vulnerability-statistics)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- Pentesting Statistics 2026: Key Insights and Emerging Trends (https://zerothreat.ai/blog/emerging-penetration-testing-statistics)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/penetration-testing/statistics)
- Foster Collaboration Between IT and Operations
- Manufacturers are making progress with AI, but barriers remain: Cisco (https://manufacturingdive.com/news/cybersecurity-top-barrier-expanding-ai-in-manufacturing-cisco/813751)
- The Importance of Cross-Training in Manufacturing in 2026 (https://bitsorchestra.com/idea/cross-training-in-manufacturing)
- New cyber strategy bets on coordination over regulation | Federal News Network (https://federalnewsnetwork.com/cybersecurity/2026/04/new-cyber-strategy-bets-on-coordination-over-regulation)
- Cybersecurity 2026: AI, CISA, manufacturing sector all in the hot seat (https://cybersecuritydive.com/news/cyber-trends-outlook-2026/810708)
- 7 Key Manufacturing Cybersecurity Trends for 2026 | Huntress (https://huntress.com/blog/manufacturing-cybersecurity-trends)

